- Ethical Hacking Statement
- The Modern Security Operations Center
- The Windows Operating System
- Linux Basics
- Network Protocols
- Ethernet and IP Protocol
- Connectivity Verification
- Address Resolution Protocol
- The Transport Layer
- Network Services
- Network Communication Devices
- Network Security Infrastructure
- Attackers and Their Tools
- Common Threats and Attacks
- Network Monitoring and Tools
- Attacking the Foundation
- Attacking What We Do
- Understanding Defense
- Access Control
- Threat Intelligence
- Public Key Cryptography
- EndPoint Protection
- Endpoint Vulnerability
- Technologies and Protocols
- Network Security Data
- Evaluating Alerts
- Working with Network Security Data
- Digital Forensics and Incidents Analysis and response
1.What is cyberwarfare?
- A. It is an attack on a major corporation.
- B. It is an attack designed to disrupt, corrupt, or exploit national interests.
- C. It is an attack that only involves robots and bots .
- D. It is an attack only on military targets.
This item is based on information contained in the presentation. Cyberwarfare is a subset of information warfare (IW). Its objective is to disrupt (availability), corrupt (integrity) or exploit (confidentiality or privacy). It can be directed against military forces, critical infrastructures, or other national interests, such as economic targets. It involves several teams that work together. Botnet might be one of several tools to be used for launching the attack.
2. What type of malware has the primary objective of spreading across the network?
- A. worm
- B. virus
- C. Trojan horse
- D. Botnet
The main purpose of a worm is to self-replicate and propagate across the network. A virus is a type of malicious software that needs a user to spread. A trojan horse is not self-replicating and disguises itself as a legitimate application when it is not. A botnet is a series of zombie computers working together to wage a network attack.
3. What is a botnet?
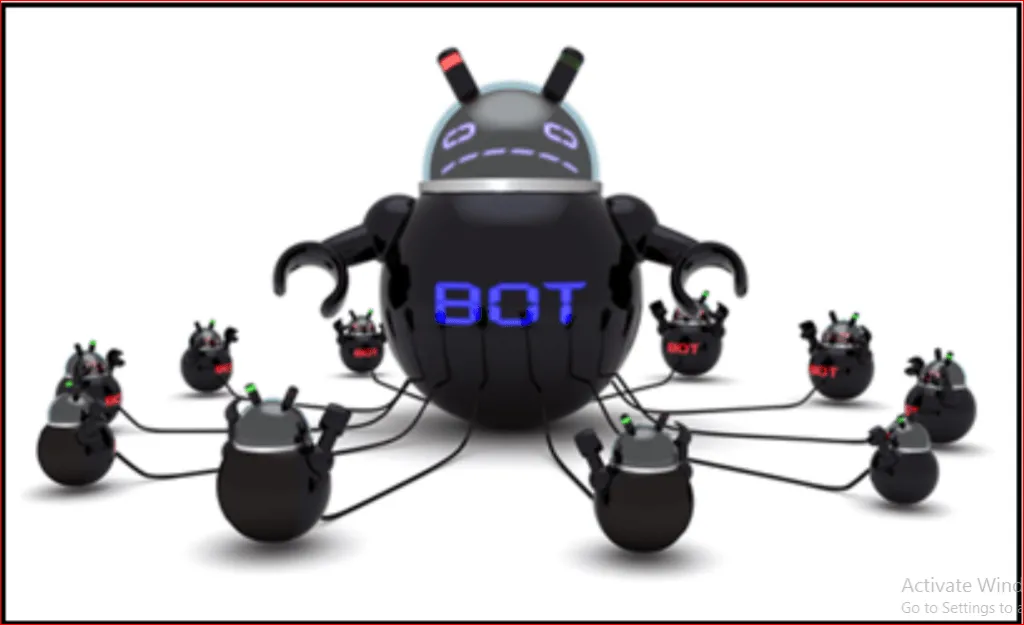
- A. An online video game intended for multiple players.
- B. A network that allows users to bring their own technology.
- C. A group of web servers that provide load balancing and fault tolerance.
- D. A network of infected computers that are controlled as a group.
One method of executing a DDoS attack involves using a botnet. A botnet builds or purchases a botnet of zombie hosts, which is a group of infected devices. The zombies continue to create more zombies which carry out the DDoS attack.
4. A company pays a significant sum of money to hackers in order to regain control of an email and data server. Which type of security attack was used by the hackers?
- A. Ransomware
- B. DoS
- C. Trojan horse
- D. spyware
Ransomware involves the hackers preventing user access to the infected and controlled system until the user pays a specified amount.
5. What name is given to an amateur hacker?
- A. Red hat
- B. Script kiddie
- C. Black hat
- D. Blue team
Script kiddies is a term used to describe inexperienced hackers.
6. What commonly motivates cybercriminals to attack networks as compared to hactivists or state-sponsored hackers?
- A. Fame seeking
- B. Financial gain
- C. Political reasons
- D. Status among peers
Cybercriminals are commonly motivated by money. Hackers are known to hack for status. Cyberterrorists are motivated to commit cybercrimes for religious or political reasons.
7. What is the best definition of personally identifiable information (PII)?
- A. Data that is collected by businesses to track the digital behavior of consumers.
- B. Data that is collected from servers and web browsers using cookies in order to track a consumer.
- C. Data that is collected from servers and websites for anonymous browsing.
- D. Data that is collected by businesses to distinguish identities of individuals.
Personally identifiable information (PII) is data that could be used to distinguish the identity of an individual, such as mother’s maiden name, social security number, and/or date of birth.
8.What is a rogue wireless hotspot?
- A. It is a hotspot that was set up with outdated devices.
- B. It is a hotspot that does not encrypt network user traffic.
- C. It is a hotspot that appears to be from a legitimate business but was actually set up by someone without the permission from the business.
- D. It is a hotspot that does not implement strong user authentication mechanisms.
A rogue wireless hotspot is a wireless access point running in a business or an organization without the official permission from the business or organization.
9. What are two purposes of launching a reconnaissance attack on a network? (Choose two.)
- A. To retrieve and modify data.
- B. To scan for accessibility.
- C. To escalate access privileges.
- D. To gather information about the network and devices.
Gathering information about a network and scanning for access is a reconnaissance attack. Preventing other users from accessing a system is a denial of service attack. Attempting to retrieve and modify data, and attempting to escalate access privileges are types of access attacks.
10. At the request of investors, a company is proceeding with cyber attribution with a particular attack that was conducted from an external source. Which security term is used to describe the person or device responsible for the attack?
- A. fragmenter.
- B. skeleton.
- C. threat actor.
- D. tunneler.
Some people may use the common word of “hacker” to describe a threat actor. A threat actor is an entity that is involved with an incident that impacts or has the potential to impact an organization in such a way that it is considered a security risk or threat.
