- CCNA Interview Questions [1]
- CCNA Interview Questions [2]
- CCNA Interview Questions [3]
- CCNA Interview Questions [4]
- CCNA Interview Questions [5]
- CCNA Interview Questions [6]
- CCNA Interview Questions [7]
- CCNA Interview Questions[8]
- CCNA Interview Questions [9]
- CCNA Interview Questions [10]
- CCNA Interview Questions [11]
- CCNA Interview Questions [12]
- CCNA Interview Questions [13]
- CCNA Interview Questions [14]
- CCNA Interview Questions [15]
- CCNA Interview Questions [16]

CCNA Interview Questions and Answers -12
1. What is Proxy ARP?
Proxy ARP is the process in which one system responds to the ARP request for the another system.
Example – Host A sends an ARP request to resolve the IP address of Host B. Instead of Host B, Host C responds to this ARP request.
2. What is Gratuitous ARP? Why it is used?
When a Host sends an ARP request to resolve its own IP address, it is called Gratuitous ARP. In the ARP request packet, the Source IP address and Destination IP address are filled with the Same Source IP address itself. The Destination MAC address is the Broadcast address (FF:FF:FF:FF:FF:FF).
Gratuitous ARP is used by the Host after it is assigned an IP address by DHCP Server to check whether another host in the network does not have the same IP address. If the Host does not get ARP reply for a gratuitous ARP request, It means there is no another host which is configured with the same IP address. If the Host gets ARP reply than it means another host is also configured with the same IP address.
3. What is Reverse ARP?
Reverse ARP is used to obtain Device’s IP address when its MAC address is already Known.
4. What is Inverse ARP?
5. What is SNMP?
The Simple Network Management Protocol (SNMP) enables a network device to share information about itself and its activities. It uses the User Datagram Protocol (UDP) as the transport protocol for passing data between managers and agents.
6. What are the Components of SNMP?
A complete SNMP system consists of the following parts:-
SNMP Manager – A network management system that uses SNMP to poll and receive data from any number of network devices. The SNMP manager usually is an application that runs in a central location.
SNMP Agent – A process that runs on the network device being monitored. All types of data are gathered by the device itself and stored in a local database. The agent can then respond to SNMP polls and queries with information from the database, and it can send unsolicited alerts or “traps” to an SNMP manager.
7. Explain MIB?
MIB is a hierarchical Database Structure for information on the device. Example – Serial numbers are in a specific location, NIC Statistics etc.
8. What are different SNMP versions?
There are different versions of SNMP – SNMP V1, SNMP V2c, and SNMP V3.
SNMP version 1 – It is the oldest flavor. It is Easy to set up – only requires a plaintext community.
SNMP version 2c – It is identical to Version 1, except that it adds support for 64 bit counters.
SNMP version 3 – It adds security to the 64 bit counters. SNMP version 3 adds both Encryption and
Authentication, which can be used together or separately.
9. I can issue a Simple Network Management Protocol (SNMP) ping to the router asking it to ping all data-link connection identifier (DLCI) partners, and it is successful. What does this indicate?
This confirms that the protocol is configured and the protocol-to-DLCI mapping is correct at both ends.
10. What is Hub?
Hub is the simplest of these devices. Any data packet coming from one port is sent to all other ports. It is then up to the receiving computer to decide if the packet is for it. Imagine packets going through a hub as messages going into a mailing list. The mail is sent out to everyone and it is up to the receiving party to decide if it is of interest.
The biggest problem with hubs is their simplicity. Since every packet is sent out to every computer on the network, there is a lot of wasted transmission. This means that the network can easily become bogged down.
Hubs are typically used on small networks where the amount of data going across the network is never very high.
11. What are advantages of using switches in Network?
Advantages of Switches:
– Switches increase available network bandwidth
– Switches reduce the workload on individual computers
– Switches increase network performance
– Networks that include switches experience fewer frame collisions because switches create
collision domains for each connection (a process called micro segmentation)
– Switches connect directly to workstations.
12. Which type address used by layer 2 switching?
Layer 2 switching uses Hardware Address (MAC Address) of devices. Media Access Control (MAC) address burned into each and every Ethernet network interface card (NIC). The MAC, or hardware, address is a 48-bit (6-byte) address written in a hexadecimal format.
13. What is the use of Spanning Tree Protocol (STP)?
The function of Spanning Tree Protocol (STP) is to prevent Layer 2 switching loop and broadcast storms in a Local Area Network (LAN). The Spanning Tree Protocol (STP) allows redundant links in a network to prevent complete network failure if an active link fails, without the danger of Layer 2 Switching loops.
14. How to bridges and switches build and maintain the filter table?
Bridges use software to create and manage a filter table, switches use application-specific integrated circuits (ASICs) to build and maintain their filter tables.
15. Why layer 2 switches and bridging are faster than router?
Layer 2 switches and bridges are faster than routers because they don’t take up time looking at the Network layer header information. Instead, they look at the frame’s hardware addresses before deciding to either forward, flood, or drop the frame.
16. What are differences between Bridging and LAN switching?
– Bridges are software based, while switches are hardware based because they use ASIC chips to help make filtering decisions.
– A switch can be viewed as a multiport bridge.
– There can be only one spanning-tree instance per bridge, while switches can have many.
– Most switches have a higher number of ports than most bridges.
– Both bridges and switches flood layer 2 broadcasts.
– Bridges and switches learn MAC addresses by examining the source address of each frame received.
– Both bridges and switches make forwarding decisions based on layer 2 addresses.
17. What is the difference between STP and RSTP?
The main difference between Rapid Spanning Tree Protocol (RSTP IEEE 802.1W) and Spanning
Tree Protocol (STP IEEE 802.1D) is that Rapid Spanning Tree Protocol (RSTP) assumes the three Spanning Tree Protocol (STP) ports states Listening, Blocking, and Disabled are same (these states do not forward frames and they do not learn MAC addresses). Hence RSTP places them all into a new called Discarding state. Learning and forwarding ports remain more or less the same.
In Spanning Tree Protocol (STP IEEE 802.1D), bridges would only send out a BPDU when they received one on their root port. They only forward BPDUs that are generated by the Root Bridge. Rapid Spanning Tree Protocol (RSTP IEEE 802.1W) enabled switches send out BPDUs every hello time, containing current information.
Spanning Tree Protocol (STP IEEE 802.1D) includes two port types; Root Port and Designated Port. Rapid Spanning Tree Protocol (RSTP IEEE 802.1W) includes two additional port types called as alternate ports and backup ports. Analternate port is a port that has an alternative path or paths to the root but is currently in a discarding state (can be considered as an additional unused root port). A backup port is a port on a network segment that could be used to reach the root switch, but there is already an active designated port for the segment (can be considered as an additional unused designated port).
18. Explain the function of layer 2 switching?
Address learning –
Layer 2 switches and bridges remember the source hardware address of each frame received on an interface, and they enter this information into a MAC database called a forward/filter table.
Forward/filter decisions –
Step – 1 When a frame arrives at a switch interface, the destination hardware address is compared to the forward/filter MAC database. If the destination hardware address is known and listed in the database, the frame is only sent out the correct exit interface. The switch doesn’t transmit the frame out any interface except for the destination interface. This preserves bandwidth on the other network segments and is called frame filtering.
Step – 2 But if the destination hardware address is not listed in the MAC database, then the frame is flooded out all active interfaces except the interface the frame was received on. If a device answers the flooded frame, the MAC database is updated with the device’s location (interface). If a host or server sends a broadcast on the LAN, the switch will flood the frame out all active ports except the source port by default.
Loop avoidance –
If multiple connections between switches are created for redundancy purposes, network loops can occur. Spanning Tree Protocol (STP) is used to stop network loops while still permitting redundancy
19. How cab we see the mac address forward-filter table of switches?
Show mac address-table – The command show mac address-table will show you the forward/filter table used on the LAN switch.
20. What is the advantage of redundant link between switches?
Redundant links between switches are a good idea because they help prevent irrecoverable network failures in the event one link stops working.
21. What is UDLD and why it is required?
UDLD is a Layer 2 protocol that enables devices connected through fiber-optic or twisted-pair Ethernet cables to monitor the physical configuration of the cables and detect when a unidirectional link exists. All connected devices must support UDLD for the protocol to successfully identify and disable unidirectional links. When UDLD detects a unidirectional link, it administratively shuts down the affected port and alerts you. Unidirectional links can cause a variety of problems, including spanning-tree topology loops.
22. How do you stop someone from simply plugging a host into one of your switch ports—or worse, adding a hub, switch, or access point into the Ethernet jack in their office?
You can stop them in their tracks by using port security.
Switch#config t
Switch(config)#int f0/1
Switch(config-if)#switchport mode access →[Change the port from desirable mode to access port]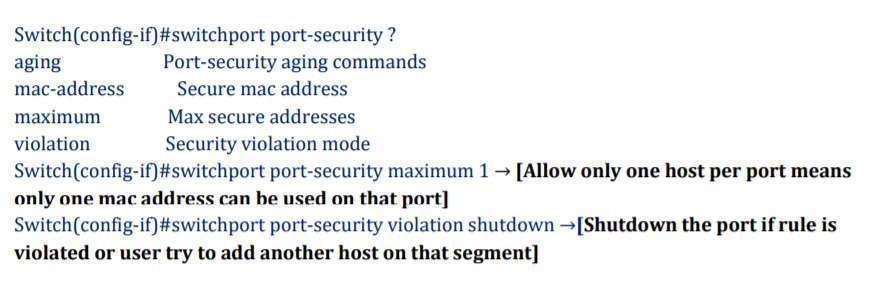 Switch(config-if)#switchport port-security mac-address sticky
Switch(config-if)#switchport port-security mac-address sticky
Switch(config-if)#switchport port-security maximum 2
Switch(config-if)#switchport port-security violation shutdown
23. What are difference between Protect Mode and Restrict Mode in Security Violation?
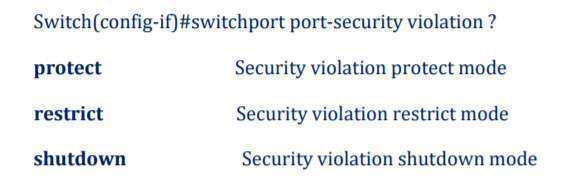
Protect Mode – Protect mode means that another host can connect but its frames will just be dropped. , no notification action is taken when traffic is dropped.
Restrict Mode – a syslog message is logged, a Simple Network Management Protocol (SNMP) trap is sent, and a violation counter is incremented when traffic is dropped.
24. What is Switching?
The function of Switching is to Switch data packets between devices on the same network.
25. What is the difference between a HUB, Switch & Router?
Hub is designed to connect hosts to each other with no understanding of what it is transferring. When a Hub receives a packet of data from a connected device, it broadcasts that data packet to all other ports regardless of destination port. HUB operates at Layer 1 (Physical Layer).
Switch also connects hosts to each other like a hub. Switch differs from a hub in the way it handles packets. When a switch receives a packet, it determines what hosts the packet is intended for and sends it to that hosts only. It does not broadcast the packet to all the hosts as a hub does which means bandwidth is not shared and makes the network more efficient. Switch operates at Layer 2 (Data Link Layer).
Router is different from a switch or hub since its function is to route data packets to other networks, instead of just the local network. Routers operates at Layer 3 (Network Layer).
26. What is Sub Interface?
To support ISL or 802.1Q routing on a Fast Ethernet interface, the router’s interface is divided into logical interfaces—one for each VLAN. These are called subinterfaces.
What is a MAC address Table and how a Switch will build a MAC table?
To switch frames between LAN ports efficiently, the switch maintains an address table called MAC address Table or CAM Table (Content Addressable Memory Table). When the switch receives a frame, source MAC address is learned and recorded in the CAM table along with the port of arrival, VLAN and time stamp. The switch dynamically builds the MAC address table by using the Source MAC address of the frames received. Than this table is used by switch to determine where to forward traffic on a LAN.
27. How Switch Learns Mac Address?
When a frame reaches to the port of a switch, the switch reads the MAC address of the source device from Ethernet frame and compares it to its MAC address table (also known as CAM (Content Addressable Memory) table). If the switch does not find a corresponding entry in MAC address table, the switch will add the address to the table with the port number at which the Ethernet frame is received.
If the MAC address is already available in the MAC address table, the switch compares the incoming port with the port already available in the MAC table. If the port numbers are different, the switch updates the MAC address table with the new port number.
28. How does Switch performs Forwarding function?
When a Layer2 Ethernet frame reaches a port on the Switch, it not only reads the source MAC address of the Ethernet frame as a part of learning function, but also reads the destination MAC address as a part of forwarding function. The destination MAC address is important to determine the port which the destination device is connected to.
As the destination MAC address is found on the MAC address table, the switch forwards the Ethernet frame via the corresponding port of the MAC address.
29. Explain Flooding?
If the destination MAC address is not found in the MAC address table, the switch forwards the frame out all of its ports except the port on which the frame was received. This is known as flooding.
30. Explain Dynamic Trunking Protocol (DTP)?
Dynamic Trunking Protocol (DTP) is a Cisco proprietary trunking protocol used for negotiating trunking on a link between two Cisco Switches. Dynamic Trunking Protocol (DTP) can also be used for negotiating the encapsulation type of either 802.1q or Cisco ISL (Inter-Switch Link).
